Frequently Asked Questions
General Questions
What is the Cybersecurity Initiatives Program?
This collaborative, national program is designed to strengthen cybersecurity at Canada’s research and education organizations by aligning, coordinating, and funding cybersecurity initiatives that are identified as priorities through extensive consultations with stakeholders across the sector.
Who funds this program?
The federal government department Innovation, Science and Economic Development Canada (ISED), is funding CANARIE to coordinate, align, and invest in the initiatives of the program.
Who can join the Cybersecurity Initiatives Program?
Participation is open to Eligible Organizations (see criteria below). Participation is limited to one application per organization.
Our organization has a cybersecurity product or service that may benefit Canada’s research and education sector. How can we propose it to be funded under the Cybersecurity Initiatives Program?
New initiatives for funding are invited to be submitted for consideration by the Cybersecurity Advisor Committee. Your initiative proposal must be sponsored by a member of the research and education community. This can include eligible organizations (see eligibility criteria here), NREN Partners, or community organizations and associations that represent eligible organizations (such as CUCCIO, CICan, etc.). For example, a proposal from a private sector entity must include at least one sponsor from the eligible list above.
To submit a proposal, please download and complete the Initiative Intake Form and submit it to [email protected]. We will follow up with you with next steps.
What are the criteria for being considered an “Eligible Organization (EO)”?
To be eligible to participate in this program, an organization must be:
- connected to the National Research and Education Network (NREN); and
- a member organization of an NREN Partner and have an autonomous network; and
- a post secondary institution, a non-federal research facility, or a Centre of Excellence.
Is there a deadline for participating in the Cybersecurity Initiatives Program (CIP)?
Eligible Organizations can apply to the program until March 31, 2023 but funding for the CIP continues to March 31, 2024. Your organization can only access funded initiatives once its participation in the CIP is confirmed. The sooner your organization participates in the CIP, the longer it will be able to benefit from the funded initiatives.
For CIP participants, is there a deadline for signing up for funded initiatives?
Yes. Each funded initiative will have a deadline for its deployment/access or for application. The deadline for deploying the first funded initiative, CIRA DNS Firewall, is March 31, 2023.
Are we obligated to implement all the initiatives funded through CIP?
There is no such obligation, but CIP-funded initiatives are intended to integrate with each other to strengthen cybersecurity at the organization level, and in turn the overall security of the entire sector.
NREN Partner Questions
What is the NREN?
Canada’s National Research and Education Network (NREN) connects Canada’s researchers, educators, and innovators to each other and to data, technology, and colleagues around the world. It also connects to a global web of more than 100 NRENs around the world, all dedicated to the unique needs of the research and education sector. Thirteen provincial and territorial partners and the federal partner, CANARIE, form Canada’s NREN.
What is the role of the NREN’s provincial and territorial partners in the Cybersecurity Initiatives Program?
The provincial and territorial partners in the NREN will work with CANARIE to communicate, lead, coordinate, and support delivery of the funded initiatives.
How is the Cybersecurity Initiatives Program related to the Canadian Shared Security Operations Centre (CanSSOC) Proof of Concept, the National Research and Education Network (NREN) SIEM project, and the ON-CHEC program in Ontario?
These are all complementary initiatives that build cybersecurity expertise, capacity, and the ability to share threat intelligence across the research and education sector.
It seems like there are a lot of national and regional security initiatives all trying to solve the same problem. Why so many initiatives?
Securing research and education is a complex challenge that requires the alignment and coordination of complementary solutions provided by different organizations. We are collaborating with other initiatives/partners toward our collective goal of securing Canada’s research and education sector.
This program is part of a broader strategy with CANARIE’s national and international partners to align to a common approach for securing the research and education sector. With this approach, all regional, national, and global cybersecurity programs available to the sector will be searchable and accessible through a central website and brand identity. More details about this new site and brand will be announced in early 2021.
Participation Obligations
What are my organization’s obligations if we join this program and execute the Organization Cybersecurity Collaboration Agreement (OCCA)?
Per the OCCA, the Eligible Organization will:
- At its discretion, select initiative(s), and for each selected initiative undertake the following, where necessary, to participate:
- Apply for, and participate in, initiative to support cybersecurity of the Organization.
- Execute additional agreement(s) for each initiative, where required.
- Participate in onboarding and training delivered by Initiative Partners.
- Participate in community collaboration related to the initiative, including online tools such as Slack.
- Identify an IT lead to undertake IT requirements specific to each initiative (support is available from the Initiative Partners where required).
- Provide feedback on potential emerging initiatives.
- Provide a final report for each initiative that the Organization has participated in, using a template provided by CANARIE.
What are CANARIE’s obligations under this program?
Per the OCCA, working with its NREN Partners, CANARIE will facilitate the delivery of cybersecurity-related projects and initiatives to Organizations [that participate in the CIP]. Those initiatives are funded in whole or in part by CANARIE.
Will my organization get direct funding through this initiative?
Some initiatives may provide funding to eligible organizations for activities such as staff training and software installation/configuration. In those cases, an additional agreement will be required between the participating organization and CANARIE. The OCCA does not provide direct funding to organizations; rather it funds initiatives that are delivered at no cost to eligible organizations.
We already have the best protections in place, and don’t see the value in implementing initiatives funded through the CIP.
CIP-funded initiatives are not intended to replace your existing protections, but to add a consistent layer of security to all organizations in Canada’s research and education sector. CIP-funded initiatives are intended to integrate with each other to strengthen cybersecurity at the organization level, and in turn the overall security of the entire sector.
For most organizations, CIP funding represents a significant cost savings to annual IT budgets that can be re-allocated to additional safeguards, training, or staff.
If your organization has already implemented the identical service as a CIP-funded initiative, participating in the CIP will automatically transition its cost to CANARIE. Once your enrolment in the CIP is complete, CANARIE will work directly with the Initiative Partner (vendor/service provider) to take over payments.
Our resources are limited, and we don’t have the time or staff to implement or maintain new initiatives.
This is where your NREN Partner comes in. Your NREN Partner staff have the expertise to act as an extension of your team. For details on the level of effort required, please review the FAQ for each initiative below.
Application Questions
How do I apply for a funded initiative?
Funded initiatives are available to eligible organizations that are participating in the Cybersecurity Initiatives Program. If your organization is eligible to participate in the CIP, the NREN Partner in your province or territory will contact you with a link to the program’s participation form. If you have questions about your organization’s eligibility, please contact your local NREN Partner.
What information is required on a participation form?
The form asks you for information that will help populate standard fields in the Organization Cybersecurity Collaboration Agreement (OCCA) with CANARIE. You can preview a sample participation form and OCCA.
Agreement Questions
What is the Organization Cybersecurity Collaboration Agreement (OCCA)?
The OCCA is an agreement between CANARIE and an Eligible Organization (EO) that has decided to participate in the Cybersecurity Initiatives Program. The Purpose of the OCCA is to formalize the Eligible Organization’s intent to collaborate and participate in national cybersecurity projects and initiatives, and benefit from CANARIE’s funding of those initiatives.
Preview a sample OCCA.
Is it possible to modify the Organization Cybersecurity Collaboration Agreement (OCCA)?
For consistency across the sector, all participants in the Cybersecurity Initiatives Program are required to execute the same agreement. The OCCA cannot be modified for individual participants.
Why do I have to execute another agreement if our institution is currently part of the Joint Security Project?
The Cybersecurity Initiatives Program is a new program, with different requirements, and requires a new agreement.
CIRA DNS Firewall
Note: Funding for the CIRA DNS Firewall and off-network protection services ends on March 31, 2026. As a result, new applications are no longer being accepted.
We already have a firewall. How is this different?
Compared to your “regular” firewall that you use to block malicious traffic coming into your network, CIRA’s DNS Firewall blocks your users from accessing malicious sites from devices within your network. A significant number of data breaches are caused by staff or students clicking on a malicious link, either through phishing or unintentional browser activity. CIRA’s DNS Firewall adds a critical layer of security by blocking access to such sites, based on a real-time and historical analysis of global threat feeds. It also identifies and reports malicious activity back to your cybersecurity team and quarantines infected devices to mitigate further risk.
We already have a DNS Firewall from another vendor. Is there a benefit to switching?
Through the CIP, CANARIE is funding the implementation of the CIRA DNS Firewall at all eligible organizations. Given that most DNS Firewalls are priced on a per-FTE basis, for most organizations, the cost savings of the funded CIRA initiative is significant and those savings can be re-allocated to additional cybersecurity resources.
How can our organization access this initiative?
Please contact your NREN Partner in your province/territory.
If your organization is already enrolled in the CIP, your NREN Partner will send you a link to the CIRA Portal where you can set up your implementation of the DNS Firewall.
If your organization is not yet enrolled in the CIP:
- Your NREN Partner will send a link for the CIP Participation Form.
- After you submit this form, CANARIE will send you an Organization Cybersecurity Collaboration Agreement (OCCA) for execution.
- Once your organization executes the OCCA, your NREN Partner will send you a link to the CIRA Portal where you can set up your implementation of the DNS Firewall.
How long does it take to implement this initiative?
Configuring your organization’s settings on the CIRA Firewall takes about an hour.
What’s the time commitment for our team to maintain the CIRA DNS Firewall after it’s been implemented?
Maintenance of the DNS Firewall is minimal and will typically be less than an hour each month.
What kind of expertise do we need on our team to implement/maintain this initiative?
A member of your IT team with access to your network DNS servers will have the expertise required to implement and maintain the CIRA DNS Firewall. If your IT team does not have the resources to implement this initiative, please contact your NREN Partner. Your NREN Partner will ensure that your organization receives the support it needs to benefit from this initiative.
Are there specific cybersecurity tools we must have in place before we can benefit from this initiative?
No. There are no minimum requirements for your organization to benefit from the DNS Firewall.
CIRA DNS off-network protection
Note: Funding for the CIRA DNS Firewall and off-network protection services ends on March 31, 2026. As a result, new applications are no longer being accepted.
What is off-network protection?
CIRA off-network protection is designed to extend the protection of CIRA DNS Firewall to wherever an organization’s users are logging on. By securing laptops, phones and tablets, off-network protection can help prepare organizations to support their users in hybrid and remote working and learning environments. This service will be funded for faculty and staff at participating eligible organizations.
Who can participate in off-network protection?
Organizations who have opted in for the CIRA DNS Firewall.
This initiative is funded for faculty and staff at participating eligible organizations, however, organizations can also choose to pay for extending to students.
How can our organization access this initiative?
Please contact your NREN Partner in your province/territory.
If your organization is already enrolled in the CIP, your NREN Partner will send you a link to the CIRA Portal where you can set up your implementation of the off-network protection. If your organization is not yet enrolled in the CIP, your NREN Partner will send you a link for the CIP Participation Form.
After you submit this form, CANARIE will send you an Organization Cybersecurity Collaboration Agreement (OCCA) for execution. Once your organization executes the OCCA, your NREN Partner will send you a link to the CIRA Portal where you can set up your implementation of the DNS Firewall and off-network protection.
How long does it take to implement this initiative?
The time required to deploy the CIRA DNS Firewall off-network protection agent will largely depend on two factors: whether an automated deployment tool (e.g., Microsoft Intune) is used and how many devices are receiving the agent. Organizations accustomed to using tools such as this should be able to implement CIRA DNS Firewall off-network protection with only a few hours of effort.
Dedicated deployment support from CIRA is available to support your implementation.
How much maintenance is required?
Maintaining the CIRA DNS Firewall off-network protection agent only requires pushing updates as they are released by CIRA; there is no configurational maintenance required in the CIRA DNS Firewall platform itself to sustain off-network protection.
CanSSOC Threat Feed
We already received the CanSSOC Threat Feed through our CIRA DNS Firewall. How is this different?
The source of threat intelligence is the same, but the level of protection offered by each is very different. The integrated CanSSOC Threat Feed is one of the intelligence sources that the CIRA DNS Firewall uses to determine which malicious DNS entries / sites to block from user access.
The direct CanSSOC Threat Feed service is ingested by your next-generation firewall to block external threats from entering your network. It provides threat protection from external sources trying to gain access to your network.
CanSSOC Threat Feed also includes monitoring and reporting services to help identify and mitigate potential threats originating from the dark web.
We already subscribe to several threat feeds. Do we still need the CanSSOC Threat Feed?
This initiative is not intended to replace threat feeds you may already have in place but to strengthen them with sector-specific intelligence. The CanSSOC Threat Feed may also contain other feeds that you subscribe to, such as the feed from the Canadian Centre for Cyber Security. The CanSSOC Threat Feed consolidates and curates several feeds, uniquely focused on risks for the research and education (R&E) sector. Due to the sophistication of today’s cybersecurity threats, a risk at one R&E organization can easily create a ripple effect for the entire sector. The Threat Feed enables Canada’s R&E sector to draw upon a collective nationally based defense to support organizations.
How can our organization access this initiative?
Please contact your NREN Partner in your province/territory.
If your organization is already enrolled in the CIP, your NREN Partner will send you a link to the CanSSOC Threat Feed selection form.
- Submit your CanSSOC Threat Feed selection.
- CANARIE will send you the CanSSOC Confidentiality Agreement to execute.
- Once the CanSSOC Confidentiality Agreement is in in place, your NREN Partner will be in touch to set up your technical implementation session so that you can begin to access the Threat Feed.
If your organization is not yet enrolled in the CIP:
- Your NREN Partner will send a link for the CIP Participation Form, where you can also select the CanSSOC Threat Feed.
- After you submit this form, CANARIE will send you an Organization Cybersecurity Collaboration Agreement (OCCA) for execution.
- Once your OCCA is executed, CANARIE will send you the CanSSOC Confidentiality Agreement to execute.
- Once the CanSSOC Confidentiality Agreement is in in place, your NREN Partner will be in touch to set up your technical implementation session so that you can begin to access the Threat Feed.
How long does it take to implement this initiative?
The technical onboarding session takes about two hours, fully guided by a representative from the NREN or CanSSOC.
How much maintenance is required?
CanSSOC has developed the Threat Feed with the intent that after a small amount of basic configuration, your organization can “set it and forget it” by using it in your end point detection devices.
What kind of expertise do we need on our team to benefit from this initiative?
The only expertise required is a firewall administrator with the skills and permission to access and make changes to your organization’s firewall.
Are there other cybersecurity tools we must have in place before we can benefit from this initiative?
No, but to maximize the Threat Feed’s value, a next-generation firewall is recommended. The CanSSOC Threat Feed readily integrates with the Cisco Firepower, Fortinet FortiGate, and Palo Alto Next Generation Firewall, but integrations with other next generation firewalls, and endpoint detection and protection devices are under development.
CUCCIO Benchmarking
What is “Benchmarking”?
Benchmarking provides an evidence-based security posture assessment that includes comparisons to other research and education organizations’ performance and to best practices. It is based both on surveys and findings from external monitoring services. It also tracks progress of the overall research and education sector against a set of best practices. Benchmarking data and reports are frequently used by organizations to plan security improvements and to promote the importance of investments in cybersecurity throughout their organization.
What is “Continuous Monitoring”?
Continuous Monitoring provides a feed of nightly security observations which provide an external view of important facets of each organization’s ongoing risks. This is particularly useful for organizations that do not have mature vulnerability management practices in place to protect their servers and other critical resources. It also provides information that research and education organizations often lack, such as detection of compromised end-user devices, vulnerabilities in remotely hosted systems, and many misconfigurations. Continuous Monitoring can reveal infected devices gone undetected, missed vulnerabilities, misconfigurations in email, web applications, and more. This type of detailed information is difficult to acquire for many organizations and beyond the resources of others.
What are “Vendor Assessments”?
BitSight can provide cybersecurity reports on over 200,000 organizations. The reports contain cybersecurity rating information and the organization’s scores against 23 risk vectors. The reports are available on request in one of two ways:
- Weekly reports for vendors used by your organization. For example, you may wish to monitor your LMS vendor’s security performance for a year.
- Ad hoc reports for vendors you are considering purchasing online services from. These are one-time reports as needed.
How does CUCCIO Benchmarking improve my organization’s cybersecurity?
Unlike security-maturity assessments that are largely survey-based, CUCCIO Benchmarking combines forensic data from external monitoring services (e.g., BitSight) with complementary participant surveys. This approach aids in contextualizing data, supports the generation of detailed results, , and helps inform your organization’s security planning and ongoing improvements. It also helps identify the methods and best practices that made a difference at other organizations.
How does the working group function?
The working group is made up of organizational representatives who receive access to the BitSight portal, receive comparative reports, complete surveys, and receive survey results. The working group also discusses results – especially in relation to security practices – and influences the evolution of the Benchmarking process. The working group uses a mailing list, document sharing site, surveys, and workshops to collaborate. Working group members have access to every organization’s Benchmarking scores and ratings but not to their detailed findings or forensic data and not to their survey responses. Working group representatives are bound by the terms and conditions of their participation to keep all organizations’ ratings and scores confidential.
Will my organization’s data and results be confidential?
BitSight is a cybersecurity rating service that provides cybersecurity ratings and scores for over 200,000 organizations. Rating and scores are available for purchase by anyone. Much of the data used in this initiative is purchased by CUCCIO from BitSight. CUCCIO cannot control who else may decide to purchase ratings and scores directly from BitSight. However, only members of the Benchmarking working group are provided access to your scores/data and they are bound to keep them confidential. Your scores will appear more broadly in some reports without being attributed to your organization. For example, working group representatives may share the final year report with their CIOs but the report will not identify specific organizations.
Presentations about the project provide broader and less detailed information on the progress of the research and education sector, again without identifying the performance of specific organizations.
CanSSOC analysts will have access to the security observations (data) that you receive each night as part of the Continuous Monitoring component of this initiative. CanSSOC analysts use the data to alert organizations about risks and threats that may impact them.
What data will I need to provide?
Much of the data will be provided via a survey, with topics including:
- Complexity index, which is derived from the number of full-time-equivalent employees and students, as well as research revenue
- Network breakout definitions based on the public IP address space of your wireless and other networks, primarily populated by user-owned devices and the rest of your campus network
- Email security
- Detecting and responding to compromised systems
- Preventing infections on wireless networks
- Multi Factor Authentication
- Security posture (larger survey based on data from Jisc, the IT infrastructure and services provider for the UK’s research and education sector)
- Vulnerability management
- Remote work security
How can my organization use Benchmarking data?
Security teams can measure their progress on best practices and risk vectors while also comparing their performance to their peers.
CIOs can use Benchmarking data to report to their executive, audit committees, and boards to help evolve their organization’s cybersecurity practices and investments.
How do I know that CUCCIO Benchmarking will be effective?
Benchmarking has already been successful in identifying a set of data-driven best practices and in helping individual organizations compare their performance in these and other areas. For example, in 2018, the Benchmarking team discovered a correlation between improved compromised device scores and the use of next generation firewalls in combination with DNS firewalls. This became a recommended practice that has been tracked every year. Similarly, the team has been tracking progress and promoting the use of multifactor authentication since 2018. CISOs and security leads at organizations frequently report that their participation has helped drive security investments and improved practices within their organizations.
We’re already participating in cybersecurity assessments and measuring our metrics. How is CUCCIO Benchmarking different?
You may already be measuring key metrics of your cybersecurity practices for items such as efficacy and performance. You may also be participating in cybersecurity assessments that analyze your organization’s cybersecurity controls and the ability of the controls to remediate vulnerabilities. These are typically performed against a framework such as NIST, or a cybersecurity standard checklist. In comparison, benchmarking is the process of comparing to a standard set by peers and links to both measurement and assessment, and to comparisons over time. For more information about the distinction between these three practices, read this blog post.
CUCCIO Benchmarking complements traditional survey-based assessments and full maturity assessments based on cybersecurity frameworks. It is not designed to replace them.
Benchmarking presents an opportunity to evaluate performance in critical areas based on evidence of risk vectors such as compromised devices, out-of-date server and desktop software, email system configurations, and more. The data is collected from over 120 proprietary and open data sources. Benchmarking also allows you to compare your performance and best practices against your peers in detail and in ways not normally available through traditional security maturity assessments.
What other organizations will have access to our Benchmarking scores/data?
CanSSOC analysts will have access to the same security observations (data) that you receive each night as part of the Continuous Monitoring feature. They use the data to alert organizations about potential risks and threats.
Working group members have access to all organizations’ Benchmarking scores and ratings but not to their detailed findings or forensic data and not to their survey responses. Working group representatives are bound by the terms and conditions of their participation to keep organizations’ ratings and scores confidential.
We’re already using another cybersecurity ratings service (e.g., SecurityScorecard). How is CUCCIO Benchmarking different?
CUCCIO Benchmarking provides ways to compare your progress to other research and education organizations and to the practices that have resulted in better performance by organizations of similar size and complexity to yours. Information is gathered via surveys that are not available from similar services. For example, this CUCCIO Benchmarking tracks adoption of multi-factor authentication, how firewalls are used to protect assets, vulnerability management practices, and more.
What are the cost savings available by participating in CUCCIO Benchmarking through CIP?
The approximate cost of purchasing licenses for Benchmarking, Continuous Monitoring, and Vendor Assessments is $4,800 annually. The cost is covered for eligible organizations that have enrolled in the CANARIE Cybersecurity Initiatives Program (CIP).
How often will we be asked to complete a survey/questionnaire?
There are two onboarding forms to complete and six short surveys. They are spaced out so that each survey is available for two weeks, often with a week or two in between. The working group provides input into what should be asked and how the surveys are structured. We anticipate the surveys will evolve as we work with the soon-to-be launched NREN Cybersecurity Assessment initiative to avoid duplication and to ensure the Benchmarking and NREN Assessment processes complement each other.
What are the technical implementation and maintenance requirements?
There are no technical implementations or maintenance requirements to participate in CUCCIO Benchmarking. Research & education (R&E) organizations of all sizes and capacities are encouraged to enroll. The more organizations that participate, the more robust the dataset and the greater the benefit to the entire R&E sector.
Who do I contact for support?
Support is provided by contacting the CUCCIO Benchmarking team directly and by sharing information within the working group of participants.
Why doesn’t CUCCIO use data from services other than BitSight?
There are several companies that provide a similar service; after a brief evaluation, CUCCIO selected BitSight in 2017. It is a comprehensive, one-stop shop that collects data from 100+ sources and collaborates with several data partners (many exclusively) who specialize in various types of telemetry.
CUCCIO is currently testing other data services as part of Continuous Monitoring and will consider using them for Benchmarking.
What kind of data does BitSight provide?
BitSight provides three types of data:
- Overall rating
- Letter grades (as well as scores out of 100) for things like botnet infections, potentially exploited systems, spam propagation, SSL configuration, patching cadence, open ports, server software, desktop software, and so on.
- Forensics data – detailed data that determine each grade. Forensics data is normally only available to the company or organization being rated. For Benchmarking, each organization provides permission for CUCCIO to download forensic data for analysis.
How do I relate BitSight data to assessments based on NIST?
Summary PDF reports and CSVs are available via the BitSight portal, which reveal your organization’s alignment with the NIST Cybersecurity Framework or with ISO 27001 that include BitSight grades.
National Cybersecurity Assessment (NCA)
What is a cybersecurity self-assessment?
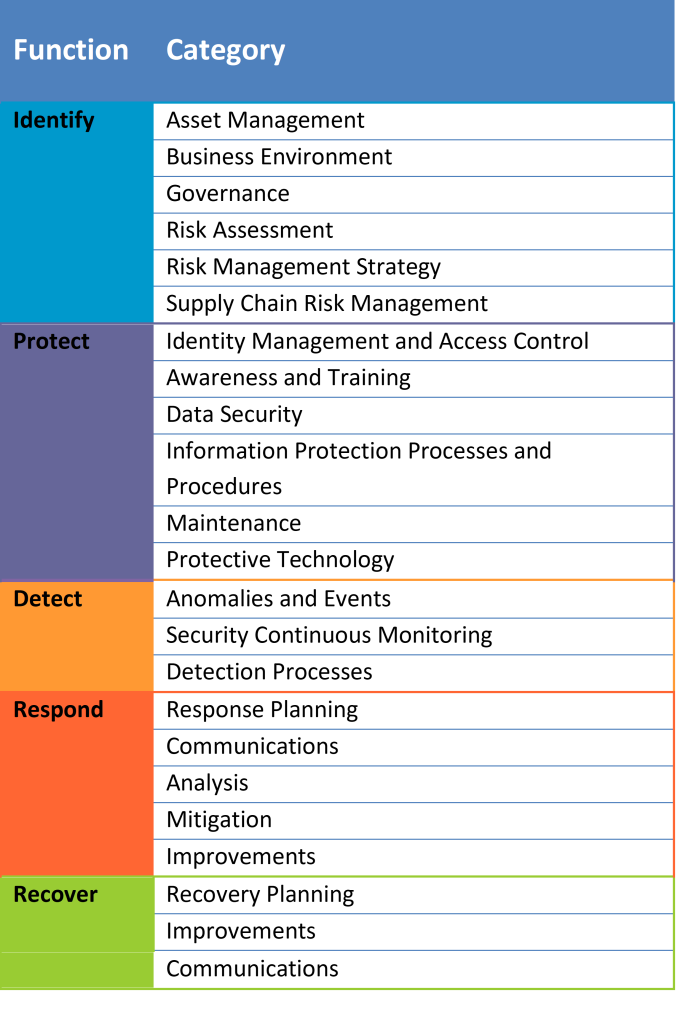
A cybersecurity self-assessment is a way of evaluating security controls to determine your organization’s overall security posture. The National Cybersecurity Assessment uses the US National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF), which is broken into 5 functions and 23 categories. The assessment asks a series of questions to determine how well your organization is doing in each category and helps identify the areas that pose the greatest risk.
The perspectives that a cybersecurity self-assessment will offer you differ from what an external cybersecurity audit or assessment reveal. An external audit is a point-in-time evaluation that verifies that specific security controls are in place. However, a cybersecurity assessment is a high-level analysis that determines the effectiveness of those cybersecurity controls to rate your organization’s overall cybersecurity maturity against an established framework (in this case, the NIST CSF).
What questions will the assessment help us answer?
The final report that your organization will receive will help answer a number of questions, including:
- What are our organization’s current cybersecurity strengths, gaps, and risks?
- What is the current maturity of our organization’s cybersecurity program?
- How does our organization measure up against an established cybersecurity framework?
- Where should our organization focus our cybersecurity spend?
- How does our organization’s cybersecurity capacity compare to similar organizations?
How is the NCA self-assessment different from the CUCCIO Cybersecurity Benchmarking service?
The NCA self-assessment uses a curated set of control questions based on the NIST Cybersecurity Framework, with a set of multiple-choice answers that follow the Capability Maturity Model Integration (CMMI) progression. By participating in the assessment, your organization gains insights into the extent to which your organization is actively and effectively addressing cybersecurity across the comprehensive range of CSF functions and is provided visual representations illustrating areas to address to enhance overall cybersecurity posture. A self-assessment using the NIST framework delves into three significant areas:
- the extent to which risk management processes are formalized and informed by organization-wide business/mission requirements, risk objectives and your threat environment
- The extent to which your organization has an integrated risk management program that supports an organization-wide approach to managing cybersecurity including the communication between senior cybersecurity and non-cybersecurity executives on cybersecurity risk
- The extent of the organization’s external participation with the broader ecosystem to inform its own and the relevant community’s (including supply chain) understanding of cybersecurity risk
Given the breadth of information covered by the questions, the process of responding to the entire set of questions generally involves gathering responses and views from a number of people across an organization rather than having a single person respond to all of the questions.
The CUCCIO Benchmarking service provides a score based on various external scans of your organization. Together, the CUCCIO Benchmarking service and the National Cybersecurity Assessment provide your organization with a comprehensive view of your cybersecurity capabilities and specific areas of strength and weakness.
How do we relate our National Cybersecurity Assessment data to our CUCCIO Cybersecurity Benchmarking scores?
The NCA and the Benchmarking services are complementary in nature.
Powered by the BitSight platform, CUCCIO Benchmarking scores come from continuous technical monitoring of the externally accessible domains associated with your organization. It can reveal configuration issues, vulnerabilities, and known breach information collected from external sources. BitSight assesses your exposed technology implementation and continuously monitors those technologies for new vulnerabilities.
The NCA service, on the other hand, is a point-in-time self-assessment based on the NIST CSF. This kind of assessment focuses less on technology and more on the maturity of the security processes of your organization. It covers items that are not directly identifiable through a technology-based assessment.
Together, the NCA and BitSight can provide a comprehensive view of your cybersecurity environment, identifying weaknesses that could increase the risk of a security incident if not mitigated. For example, BitSight may provide evidence that your external presence is vulnerable to an attack because it has not been patched. This may lead to the understanding that your patch management and IT security processes are not performing as expected.
Conversely, for example, the NCA may reveal that your business continuity maturity is low, which increases the risk of a longer-than-desired outage in the case of a cybersecurity event.
How does the National Cybersecurity Assessment service make my organization more secure?
The National Cybersecurity Assessment identifies gaps and areas of priority for each participating organization. The report provided will include recommended steps your organization can take to immediately improve its security posture, or to better define a long-term cybersecurity roadmap.
The assessment will help you determine your security gaps and overall risk. By participating, your organization will have a better understanding of your areas of strength and weakness, which may help mitigate your risk of a security event.
Why is this assessment based on the NIST Cybersecurity Framework (CSF)?
The Government of Canada, through the Canadian Centre for Cyber Security, made the decision to include the academic sector as one of the sectors of Canada’s Critical Infrastructure to be secured against cybersecurity threats. The NIST Framework is the top cybersecurity framework primarily intended to support the management and mitigation of cybersecurity risk in critical infrastructure organizations.
Even though there are multiple other frameworks in use throughout the post-secondary sector, the NREN selected this central framework for a nationally consistent approach among all participants, and to support funding opportunities in functions (Identify, Protect, Detect, Respond, Recover) where common gaps are identified.
What data will I need to provide?
Personally identifiable information (PII) is not required to participate in the NCA. The following data is required:
- Basic contact information (first name, last name, email address) for the individual who will be considered the “questionnaire owner” at your organization. This information is required to set up an account on the Alyne platform, which is used for the NCA questionnaire.
- Data required to calculate your organization’s placement relative to the global complexity index, including student FTE, staff FTE, and research revenue.
- Responses to the multiple-choice questions in the assessment itself.
How can my organization use the reports produced by the NCA?
Organizations will receive three different types of outputs, prepared by the NREN’s National Service Team of cybersecurity analysts:
- Report of Assessment Results and Recommendations
Target Audience: Presidents, Boards of Directors, CISOs, Risk Managers, VPs Research, Provosts, Security Teams, CIOs, Vice Presidents of Finance and Administration, Risk and Audit Committees
A high-level summary of the assessment results, including your organization’s maturity level compared to the overall expected maturity level and the five NIST CSF functions, your organization’s top three assessed risks, and recommendations to address those risks.
- Comparative Report
Target Audience: Security Teams, CIOs, VPFAs and other executives, Risk and Audit Committees
Visual representations and graphs to allow you to compare your organization to your peers (per the Global Complexity Index).
CIOs can use the two reports above to help prioritize security investments, and to raise awareness of cybersecurity gaps at the executive level and with other stakeholders.
- Raw data
Target Audience: Security Teams and CIOs
A PDF and Excel file of the raw assessment data is available in the Alyne platform. Your security team may choose to use this data for its own analysis and to identify strengths and gaps.
We’re already participating in an annual assessment required by our insurance provider. How is this assessment different?
Insurance providers use questionnaires to help determine the risk to them in offering cyber insurance to potential customers. They ask targeted questions that do not cover the full spectrum of a security program. This assessment is designed to help participants gain an appreciation for the full spectrum of cybersecurity functions, and their organization’s maturity for each. The intent is that your organization will be able to identify and fill priority gaps prior to being required to by an insurance provider or auditor.
What will our cost savings be by participating in the National Cybersecurity Assessment, funded through CIP?
Organizations will save the cost of purchasing a license for a cybersecurity assessment platform, as well as the staff time to extract the data from the tool to determine the risk areas. The service will also offer your organization training, support, and insight over and above what you would receive from simply conducting the assessment on your own.
Having a comprehensive understanding of your cybersecurity posture and taking the steps to mitigate gaps or weaknesses could help mitigate a cyber-attack or data breach. The estimated average cost of each data breach was $7.44 M in Canada in 2021 (Source: Cost of a Data Breach 2022 Report | IBM).
How often will we be asked to complete a questionnaire?
Eligible organizations will be asked to complete a questionnaire once a year within a standardized timeframe.
What are the technical implementation and maintenance requirements?
There are no technical implementations or maintenance requirements to participate in the NCA. Research & education organizations of all sizes and capacities are encouraged to participate. The more eligible organizations that participate, the more robust the dataset that informs regional and national decisions and approaches, which in turn amplifies the benefits delivered to your organization.
Who do I contact for support?
Support is provided by contacting the NCA National Service Team directly through [email protected]. A resource library containing self-serve documentation and video tutorials is available at https://nca.nren.ca.
How many questions are in the assessment questionnaire?
There are 240 control questions encompassing all five functions (identify, protect, detect, respond, recover) of the NIST CSF.
How long will it take to complete the assessment questionnaire?
This will vary depending on extent that you need to consult with other groups or colleagues in your organization to provide accurate and informed answers to certain questions. In such cases, you can either choose to engage with those individuals directly (either through consultation or organizing a group meeting) or to distribute responsibility for completing portions of your assessment questionnaire to others, using the delegation function in the Alyne platform.
If a single individual at your organization has all the answers to the 240 self-assessment questions, it would be possible to complete the assessment in less than a day. However, the questionnaire touches on several aspects of your organization, so it is unlikely that a single individual to be able to answer all the questions.
When will our assessment reports be available to us?
All the reports will be distributed three months after the assessment deadline. However, given the Service Delivery Team will be developing each of the reports individually, the ‘Assessment Results and Recommendations’ report may be delivered to participants earlier if the assessment questionnaire is completed and submitted well in advance of the deadline.
Why is the Alyne platform being used for the NCA?
Following a rigorous RFP process to evaluate a platform for this service, Alyne was selected by the NREN Partners as it best met the needs of this national assessment.
What is the deadline for completing the NCA questionnaire?
To ensure that the aggregate assessments of all participating organizations are included in NCA reports, the questionnaire must be completed by midnight ET on December 15, 2023.
What other organizations will have access to our assessment scores/data?
A key value of the National Cybersecurity Assessment (NCA) is that each participating organization will gain insights about how its cybersecurity maturity compares to the cybersecurity maturity of similar organizations. This data will be sufficiently aggregated so as to maintain the confidentiality of each individual organization participating in the assessment.
Will my organization’s data and results be confidential?
Data confidentiality will be strictly maintained. All individuals handling your data will be bound by CANARIE’s Confidentiality Agreement. Furthermore, an Appropriate Use Policy will govern data storage, dissemination, and access as well as the use of data to help make data-driven decisions that support the critical needs of Canada’s research and education sector.
I’m putting very sensitive information into this assessment. What kind of security considerations have been reviewed?
Security considerations were prioritized during the national procurement process to acquire a platform to support the NCA service. Alyne’s HECVAT (Higher Education Community Vendor Assessment Toolkit) report was reviewed by the procurement committee, which included CISOs and other security professionals representing Canada’s higher education sector. All NCA data is stored in Canada, proof of data residency has been verified by the NCA Technical Lead, and security ratings of Alyne and of its platform (provided by prominent security risk tools) have been reviewed by CANARIE.
All NCA National Service Team members are bound by both a Confidentiality Agreement and an Appropriate Use Policy that outlines the requirements and limitation of use, dissemination, and storage of NCA data.
There are numerous self-assessment options available, offered by insurers, government agencies, the private sector, etc. What is unique about the NCA?
The National Cybersecurity Assessment (NCA) offered by Canada’s NREN partners has been specifically designed and developed for Canada’s research and education sector and is available at no cost to all eligible organizations participating in CANARIE’s Cybersecurity Initiative Program (CIP). The NCA will provide a comprehensive view of your organization’s cybersecurity maturity, encompassing all NIST Cybersecurity Framework functions, categories, and subcategories. It does not require you to provide any details regarding your technical infrastructure or breach history.
Beyond an assessment tool, the NCA is a service that is complemented by ongoing training and support offered by cybersecurity analysts on the NREN’s National Service Team. By participating in the NCA, you will receive a personalized report for your organization that not only identifies detailed risks, strengths, and gaps, but also provides guidance on where to make the most critical and impactful investments. In addition, these personalized reports will allow you to compare your organization’s cybersecurity practices and capabilities in relation to comparable organizations, based on the global complexity index (the same classification used in other CIP initiatives, such as the CUCCIO Benchmarking service). The NCA will be conducted on an annual basis, allowing answers from previous assessments to be brought forward and included as comparative data in your future reports.
At the provincial and federal levels, the aggregate information collected through the NCA will build a unified view of the sector to help set priorities for the investment and development of new services.

